Beyond the Blacklist: Why Behavioral AI is the New Standard for Endpoint Security
- Shilpi Mondal

- 2 days ago
- 5 min read
SHILPI MONDAL|DATE: MARCH 26,2026
If you’re still relying on traditional antivirus, you’re essentially guarding your front door with a "Most Wanted" poster from 1998. It’s a sobering thought, but in a world where malware can mutate its own code every 15 seconds, a static list of known threats is about as effective as a screen door on a submarine.
According to Sasa Software's 2025 analysis on Zero-Day Malware, the average gap between initial infection and discovery reached a staggering 208 days by mid-2024. For a CIO or IT Director, that’s not just a statisticit’s an unacceptable window of exposure. AtIronQlad, we’ve watched this "structural obsolescence" of signature-based defense move from a technical hurdle to a full-blown enterprise crisis.
The Death of the "Digital Fingerprint"
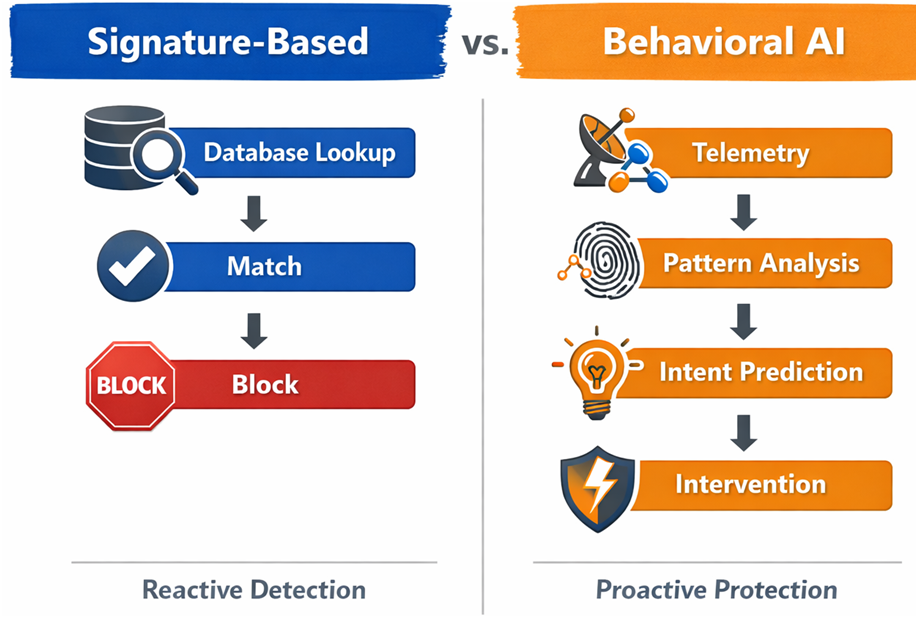
The traditional security model was deterministic, relying on known file signatures or “hashes”essentially digital fingerprintsto identify threats. If a file didn't match a known malicious signature in the database, it got a free pass. It's a clean system in theory but it rests on a assumption that has aged poorly: that you can only stop what you've already seen before.
Modern attackers figured out how to break that logic a long time ago. Polymorphic and metamorphic code doesn't sit still it rewrites its own structure on the fly, often fast enough to look brand new by the time a scanner checks it. Static signature databases are essentially playing catch-up against threats that mutate faster than any update cycle can match. So the thinking has had to shift. Rather than asking who is this file trying to match it against a known face in a wanted posterthe more useful question has become what is this file actually doing. That behavioral lens is increasingly where the real detection work happens.
From Identity to Intent: The Rise of Behavioral AI
When we talk about AI-driven antivirus, we’re really talking about a shift to intent-based security. Instead of looking at what a file is, we monitor what it does.
Think of it as a digital immune system. According to research published in the International Journal of Innovative Research in Multidisciplinary Physical Sciences, behavioral engines monitor sequences of system calls and API interactions in real-time. If a standard Word document suddenly tries to inject code into a system process or launches a PowerShell scriptbehaviors documented as red flags by Palo Alto Networksthe AI intervenes in milliseconds.
We’re also seeing the emergence of User and Entity Behavior Analytics (UEBA). As Unanimous AI highlights in their 2026 cybersecurity outlook, these systems learn your "Digital Rhythm Signature"your unique typing cadence and navigation patterns. Even if an attacker steals valid credentials, they can’t steal the "rhythm" of how you work. If the rhythm is off, the system locks down.
The Offensive AI Arms Race
It's worth being honest about something that doesn't always get enough airtime: the bad guys have access to the same tools we do. And in 2026, we've moved well past the phase where threat actors were simply tinkering with LLMs out of curiosity they've operationalized them. Google Cloud's Mandiant report on AI risk found that roughly 8% of modern malware now incorporates AI at runtime for "just-in-time" code generation. What that means in practice is that even low-skill attackers can spin up convincing lures and sidestep traditional defenses with relative ease. Arctic Wolf's latest research documented developers actively using models like DeepSeek R1 to debug and refine malicious scripts a reminder that the barrier to entry for sophisticated attacks keeps getting lower.
However, AI isn't a magic wand for attackers. It often leaves "hallucinations" or tutorial-style markers in the codelittle breadcrumbs that our behavioral detection models are trained to sniff out.
Moving Toward the Self-Healing Enterprise
The ultimate goal for any modern IT landscape is what we call the "Self-Healing Enterprise." In this model, the Security Operations Center (SOC) doesn’t wait for a human to click "Resolve."
As FutureCISO explains in their 2026 autonomous AI report, we are moving toward "Holographic Protection," where security is embedded directly into the data layer. By utilizing reinforcement learning, systems can dynamically adjust their response. If a breach occurs, the system doesn't just block a port; it might choose to segment the network or roll back a specific machine to a "clean" state automatically.
This level of automation is why platforms like SentinelOne's Singularity and CrowdStrike's Falcon have become the gold standard. Whether it’s CrowdStrike’s "Charlotte AI" analyst or SentinelOne’s offline "one-click rollback," the focus is on reducing the Mean Time to Clean Recovery (MTCR).
Predictive Threat Intelligence: Catching the Storm Before it Breaks
We're also helping clients transition to Predictive Threat Intelligence (PTI). Traditional intelligence is reactiveit looks at IPs that have already been used for an attack. PTI, however, looks for Indicators of Attack (IOA).
According to SentinelOne's cybersecurity 101 on PTI, these systems aggregate data from dark web monitoring and global telemetry to find subtle correlations. For instance, Google recently deployed Gemini agents that crawl over 10 million dark web posts daily with 98% accuracy to identify organization-specific leaks before they are exploited.
The Reality Check: Challenges and Adversarial AI
It’s not all smooth sailing. The "black-box" nature of deep learning can be a hurdle for compliance-heavy industries. That’s why we advocate for eXplainable AI (XAI). As noted in MDPI’s review on insider threat detection, XAI provides a human-readable "why" behind every detection, ensuring your analysts aren't just following a machine blindly.
Then there's a subtler threat that deserves more attention: adversarial poisoning. The concept is straightforward but the implications are serious attackers quietly corrupt the training data that security models learn from, embedding hidden backdoors that can be triggered later. Defending against it isn't simple. Palo Alto Networks advocates for what they call adversarial training, a process of deliberately exposing AI systems to controlled attacks during development so they build up a kind of immunological memory. The goal is to make sure that when a real attack comes, the model has already seen something like it before.
Strategic Roadmap for 2026
So, where does this leave your organization? If you’re reviewing your security stack this quarter, here is how we recommend prioritizing your investments:

Prioritize Intent over Identity: Stop leaning on tools that are built around signatures they're fighting yesterday's war. Make sure your AI-driven antivirus can actually contend with fileless and polymorphic threats, and that behavioral analysis is doing the heavy lifting.
Adopt Continuous Authentication: Passwords alone aren't holding the line anymore. Behavioral biometrics the kind of passive, continuous verification that the "Digital Rhythm Signature" approach represents is where identity protection needs to go.
Invest in "Digital Vaccination": Threat intelligence is only useful if it moves fast enough to matter. Look for platforms that can push global threat data to your local endpoints in minutes, not the days that most legacy pipelines require.
Measure Resilience, Not Just Prevention: At some point, something will get through that's not pessimism, it's just an honest read of the landscape. The metric worth obsessing over isn't whether an incident happens, but how quickly you recover from one. Know your MTCR (Mean Time to Clean Recovery) and treat it like the business-critical number it is.
The future of antivirus isn't a smarter version of the same old scanner. It's an autonomous, adaptive system built to move at the pace of modern threats not lag behind them. IronQlad, alongside specialized partners like AmeriSOURCE and AQcomply, is here to help you build toward that self-healing, AI-resilient enterprise.
KEY TAKEAWAYS
Signature-based detection is dead: With zero-day malware remaining undetected for over 200 days, reactive "blacklists" are no longer sufficient.
Behavioral AI is the baseline: Modern security must focus on "intent" (what a process is doing) rather than "identity" (what a file is).
Identity is continuous: The rise of "Digital Rhythm Signatures" allows for constant authentication based on user behavior, not just static credentials.
Automation is non-negotiable: To counter AI-speed attacks, organizations must move toward autonomous remediation and self-healing SOC architectures.




Comments