Triple Extortion Ransomware: The Cyber-Threat That Hits You From All Sides
- Swarnali Ghosh

- Feb 6
- 5 min read
SWARNALI GHOSH | DATE: FEBRUARY 03, 2026
Introduction

Imagine coming into the office to find your systems are encrypted. Now that could be a nightmare, but your team is ready for this because you have off-site backups. But then a text message pings on your phone. It isn’t a text from your IT department. It’s a threat actor who has just messaged your spouse and board members that they will leak sensitive HR files unless you pay within an hour. This is not a scene from a techno-thriller; it is the reality of triple extortion ransomware, an attack string that has turned traditional data breaches into a psychological war on multiple fronts.
After analyzing all the breaches, the number of ransomware attacks has increased to 44% in 2025, as per the Verizon report. It was just 7% in 2024. However, it is not simply the rate that matters, but the change in tactics. With organizations improving faster to restore from backups, attackers switch to more aggressive tactics to ensure payday.
Beyond Encryption: The Triple Extortion Playbook
For several years, the background of the cybercriminals were simple: they lock the files and sell the key. We called that a single extortion. But it didn't stop there. Before they even locked down the data, they'd already stolen it, and now they were holding it over everyone's heads, threatening to spill it all if the ransom wasn't paid. Now we are looking at a third layer targeting business continuity and personal privacy.
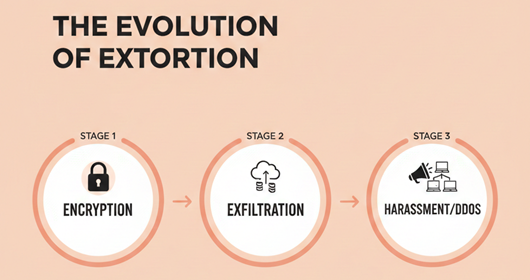
In the world of triple extortion ransomware, the attacker adds a third "squeeze" to the process. This usually takes one of two forms:
DDoS Attacks: Flooding your public-facing servers to take your website or customer portals offline while you’re already struggling with internal recovery.
Direct Harassment: Contacting your customers, employees, or even the CEO’s family members to create an unbearable "pressure cooker" environment.
As the Fortinet 2025 Ransomware Statistics Report points out, roughly 20% of ransomware incidents now involve some degree of victim harassment. That’s a massive jump from the 1% we saw just a few years ago. Why the change? Because it works. When encryption fails to move the needle, psychological warfare often does.
When it Gets Personal: The Rise of Victim Harassment
Here’s the thing that keeps CIOs up at night: these attackers aren't just faceless entities behind a screen anymore. They're researchers. They spend weeks inside your network, not just looking for data, but looking for leverage.
Targeting the C-Suite and Beyond: We’ve seen cases where threat actors send threatening SMS messages to the spouses of executives. The goal is to move the conflict from the "business" column to the "personal" column. If the CFO isn't budging on a $2 million payment, maybe they'll reconsider when their partner is receiving threats at home.
Weaponizing Customer Trust: In some of the most "chilling" examples, attackers have bypassed the company entirely to go after the customers. According to research cited in the Unit 42 2025 Global Incident Response Report, attackers are increasingly using "high-touch" tactics. One noted example is Vastaamo, where the attacker sent them all an email in which they demanded a small amount of Bitcoin from 30,000 patients to stop putting their private psychiatric notes on the dark web. It was a lot more than a data breach it was a national mental health crisis, a public health crisis that requires immediate intervention by the government.
"Attackers are no longer just stealing data; they are actively taking down entire operations and destroying reputations through targeted harassment." — Philippa Cogswell, VP at Unit 42, as quoted in CXOToday’s 2025 analysis.
The Economic Reality of the "Pressure Cooker"
You may be thinking, “Is any of this really working?” The data is not all black and white. On one hand, the 2025 Sophos State of Ransomware report noted that the average ransom payment actually took a dip in 2025 — dropping down to around $1 million, which is a pretty significant drop from the $2 million mark seen the year before.

Here's a more natural version:
But yeah, don't let those numbers trick you into thinking everything's suddenly fine. The Verizon 2025 DBIR notes that 64% of victims are actually saying no now, which is a pretty big jump from the 50% we saw just two years ago. And that's exactly why attackers are getting more creative. If they can't squeeze $2 million out of a company, they'll just go after the customers instead, maybe hit 10,000 people for $500 each. At the end of the day, it's all about the numbers for them.
Building a Multi-Extortion Defence Strategy
If your current incident response plan only covers "restoring from tape," it's time for an update. At IronQlad, we've helped countless enterprises navigate these waters, and the focus is shifting from pure "IT recovery" to "organizational resilience."
The Multi-Extortion Playbook: Your IR plan needs a section specifically for harassment. Who handles the press? How do you notify employees that they might receive threatening calls? If a DDoS attack hits while you’re recovering, do you have a secondary communication channel for customers?
Zero Trust is Non-Negotiable: You can't steal what you can't find. Implementing a Zero Trust architecture, as recommended in the Exabeam 2025 Ransomware Trends Report, limits an attacker’s ability to move laterally through your network. If they’re stuck in a single VLAN, they can't get to the sensitive HR files or the CEO’s contact list.
Data Minimization: Honestly, it's one of the simplest things you can do, and it's probably the most effective tool we've got. If you're not actively using that patient data from 10 years ago or those sensitive meeting transcripts, just get rid of them. Think about it; the less data you're sitting on, the less the attacker actually has to work with.
Staff "Harassment" Training: We’ve all completed phishing simulations. Now, it’s time to ready our employees for the “phone call” simulation. Employees must understand what to do if a threat actor calls their desk or personal cell phone. The fact that a plan is in place will remove the panic that these attackers instil.
Final Thoughts: Remaining Grounded in the Chaos
The goal of triple extortion ransomware is to create chaos. By attacking you on all technical, financial, and psychological fronts at once, the attackers are counting on you to make a quick, emotional choice to pay up.
But as we've seen at IronQlad, being prepared is the best cure for panic. When you have a strategy that takes into consideration the human factor, you put the power back in your court, not in the extortionist's.
The reality of the threat environment in 2026 is that it is certainly more aggressive, but it is not insurmountable. It simply demands that we be as calculated in our defence as they are in their attacks.
So yeah, if you're looking to put together a solid defence strategy that actually covers all your bases, it's definitely worth checking out what IronClad can do for you.
KEY TAKEAWAYS
Triple extortion is the new baseline: These days, attackers aren't just relying on one trick. They're combining encryption with data theft, and on top of that, throwing in harassment and DDoS attacks against third parties too, basically doing everything they can to crank up the pressure as much as possible.
Psychological warfare is increasing: Harassment incidents have surged from 1% to 20% of all attacks as organisations improve their backup recovery.
Personalized targeting: C-suite families and individual customers/patients are now frequently targeted to force a payout through emotional distress.
Defence must be holistic: Traditional backups are insufficient; organizations need Zero Trust, data minimization, and specific crisis communication protocols.




Comments