Cyber Resilience Strategy in Geopolitical Threat Era
- Minakshi DEBNATH

- Apr 11
- 6 min read
MINAKSHI DEBNATH | DATE: MARCH 18, 2026

the world of enterprise IT, we’ve spent decades obsessed with the "perimeter." We built digital moats, thickened our castle walls, and convinced our boards that a locked gate meant a safe kingdom. That thinking hasn't just aged poorly it's collapsed under the weight of a threat landscape that plays chess while we were still guarding the drawbridge. This is where a modern cyber resilience strategy begins to replace outdated perimeter-based thinking. Recorded Future's analysis of the 2025/2026 threat landscape analysis uses one word to describe the current geopolitical environment: shattered. It's the right word.
Peace and conflict used to be opposites. Now they share the same address. The attacker hitting your network might be a criminal crew, a nation-state, or an entity that genuinely functions as both hired for plausible deniability, funded for strategic purposes.
That's the grey zone. And in 2026, we're all operating inside it. Operating in this environment requires a clearly defined cyber resilience strategy, not just reactive security measures.
For anyone sitting in the C-suite or steering a transformation programme, this changes the core question. We've spent years asking how do we stop the breach? That was the cybersecurity era. What 2026 demands is a different question entirely: how do we survive it? Cyber resilience isn't a product you buy or a policy you file. It's a reckoning. A well-built cyber resilience strategy shifts the focus from prevention to survival and continuity.
It means accepting that the breach may come and building an organisation that bends without breaking. That recovers without collapsing. That keeps the business standing not because the walls held, but because you planned for the moment they didn't.
That's a different conversation than cybersecurity. And in 2026, it's the only one worth having.
The Mindset Shift: From Defensive Walls to Operational Muscle
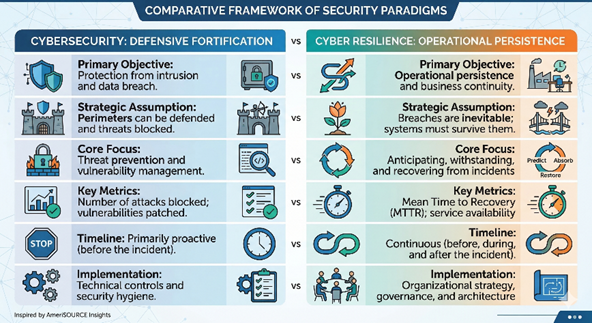
I often get asked by clients what the "real" difference is between these two terms. It’s not just semantic hair-splitting. Cybersecurity is your shield it’s the firewalls and MFA we use to block 99% of the noise. But cyber resilience? That’s your organization's central nervous system. It’s the ability to take a punch, keep breathing, and stay standing while you’re healing. This distinction is exactly where a cyber resilience strategy becomes a business-critical capability.
As Fortinet’s 2026 Resilience Guide points out, resilience assumes the adversary is already inside. While cybersecurity focuses on protection, resilience focuses on operational persistence. It’s a transition from "Can we stop them?" to "How do we keep the business running when they get in?"
"Cyber resilience addresses the ability of an organization to anticipate, withstand, recover from, and adapt to adverse conditions... ensuring essential functions persist even when infrastructure is compromised." CSIS Report on Federal Cyber Resilience
Geopolitical Fragmentation and the "Access-First" Model
We’re seeing a massive shift in how nation-states operate. We’ve moved away from loud, destructive attacks toward "pre-positioning." Think of it as battlefield preparation. Adversaries like "Salt Typhoon" aren't trying to crash your servers today; they’re quietly embedding themselves in edge infrastructure to hold your operations at risk for a future date. Without a strong cyber resilience strategy, organizations struggle to respond effectively in this blurred threat landscape.
According to SecurityWeek’s 2026 Cyber Insights, attribution isn't just difficult anymore it's become a deliberate weapon. The gap between a state actor and a criminal proxy has narrowed to the point where the distinction barely holds up under scrutiny. Take a ransomware hit on your supply chain. On the surface it looks opportunistic someone chasing a payout. But pull the thread and you might find something else entirely: a calculated move designed to fracture regional stability, with the ransom demand serving as cover. The cash grab is the costume. The disruption is the point.
This is what makes the grey zone so disorienting for leadership teams. Your response strategy can't hinge on knowing exactly who pulled the trigger because in 2026, you might never find out.The attacker's identity has become a luxury answer. What leadership needs instead is an unconditional one: we respond, we recover, we continue regardless of who's responsible. Attribution is a forensics problem. Resilience is a survival skill. Know which one your business actually needs to solve.
Here is the 2026 Threat Reality
State Actors: Focus on long-term pre-positioning in Critical National Infrastructure (CNI).
Criminal Proxies: Provide states with plausible deniability while disrupting rivals.
Hacktivists: Focus on perception warfare and amplifying chaos.
The Industrialization of AI Exploitation

2024 was our GenAI playground. 2026 is their production environment.Agentic AI has handed attackers something genuinely new: autonomous systems that plan, probe, and execute multi-step attacks without a human in the loop. No operator waiting on the other end. No pause between reconnaissance and strike. The numbers are staggering. Technology First reports that phishing attacks skyrocketed by 1,265% recently, driven almost entirely by AI’s ability to craft perfect, personalized lures. We’re also seeing a "synthetic identity crisis" where deepfakes are used to bypass biometric checks or trick finance teams into unauthorized wire transfers. This is why integrating AI into a cyber resilience strategy is no longer optional, it’s essential.
To fight back, we’re helping AmeriSOURCE clients move toward Zero Trust AI Security. Seceon’s 2026 Comprehensive Guide puts a number on it: organisations running AI-driven Zero Trust architectures saw a 76% reduction in successful breaches. That's not a marginal gain that's a structural shift.
The reason is behavioural. These systems don't just monitor access; they read patterns. A typing rhythm that's slightly off. An API call that doesn't belong. Signals a human analyst might miss or catch too late. Acted on in real time, they compress Mean Time to Detection from months the industry's quiet shame down to minutes. Zero Trust was always the right philosophy. AI is finally making it fast enough to matter.
Engineering for Survivability
So, how do you actually build this? At IronQlad, we look at resilience through the lens of the NIST SP 800-160 Vol. 2 framework. At its core, this framework is the foundation of a scalable cyber resilience strategy. It breaks down into four simple but difficult goals:
Anticipate: Use threat modeling to see the punch coming.
Withstand: Use micro-segmentation so a breach in one department doesn't kill the whole company.
Recover: Have immutable backups and a "clean room" restoration plan.
Adapt: Don't just go back to normal; learn from the incident to evolve your architecture.
Resilience is a Boardroom Conversation
Here’s the thing: you can’t buy cyber resilience in a box. It’s a governance issue. According to Deloitte’s insights on operational resilience, board-level engagement is the single biggest predictor of whether a company survives a major attack.
Boards shouldn't be asking about firewall logs. They should be defining "Impact Tolerances"the exact amount of time a business service can be down before it becomes an existential threat. They need to understand their "crown jewels" and ensure the budget follows the risk, not just the latest trend. A mature cyber resilience strategy must be owned at the board level, not just within IT teams.
The Human Factor: AI as a Force Multiplier
Finally, we have to talk about people. The skills gap is still here, but the solution has changed. We shouldn't be asking our analysts to do "grunt work" that AI can handle. Ultimately, a forward-looking cyber resilience strategy defines how organisations endure and evolve through disruption.
As CSO Online highlights, building a resilient workforce means using AI to automate the boring stuff (like alert triaging) so your humans can focus on high-level strategy and threat hunting. We need to protect our teams from burnout; an exhausted security team is a security vulnerability.
Staying Resilient in a Fractured World
The "old ways" of digital security were about building walls. The "new ways" are about building agility, intelligence, and the sheer will to persist. In an age of geopolitical instability, your ability to bounce back is the only metric that truly matters.
Whether it’s preparing for Quantum Readiness by adopting crypto-agility or securing your supply chain through Software Bills of Materials (SBOMs), the time to pivot is now. All of these principles come together to form a robust cyber resilience strategy for 2026 and beyond.
Ready to harden your organization’s "muscle" and move beyond simple defense? Explore how IronQlad, can support your journey toward total digital resilience.
KEY TAKEAWAYS
Assume the breach comes: Stop optimising purely for prevention. Build for continuity what keeps the business running during and after an incident is now as important as what keeps attackers out.
Let AI defend against AI: Agentic threats need autonomous defences. Behavioural-based Zero Trust isn't a nice-to-have anymore; it's the architecture gap between you and the next headline.
Make resilience a board conversation: Not an IT budget line. A strategic risk decision with clearly defined tolerances for what the business can absorb and for how long.
Supply Chain Visibility: SBOMs and real-time telemetry aren't compliance exercises. They're the only way to know what's running in your environment including the parts you didn't write.




Comments